User and guest IDs
If you are have a user ID in a customer tenant then follow this page to configure Partner Admin Link. This is the primary use case covered in the Microsoft Learn docs but included here for completeness.
Table of Contents
In brief
-
Authenticate in the customer context:
- sign on as the user the customer created for you in their tenant, or
- if invited as a guest into their tenant then a) sign on and b) switch directory to the customer tenant
-
Link your ID to the PartnerID using the CLI, PowerShell or the Azure Portal screen.
The information here is lifted straight from the main documentation which is found at https://aka.ms/partneradminlink.
Creating the Partner Admin Link
When you have access to the customer’s resources, use the Azure portal, PowerShell, or the Azure CLI to link your Partner ID to your user ID. Link the Partner ID in each customer tenant.
-
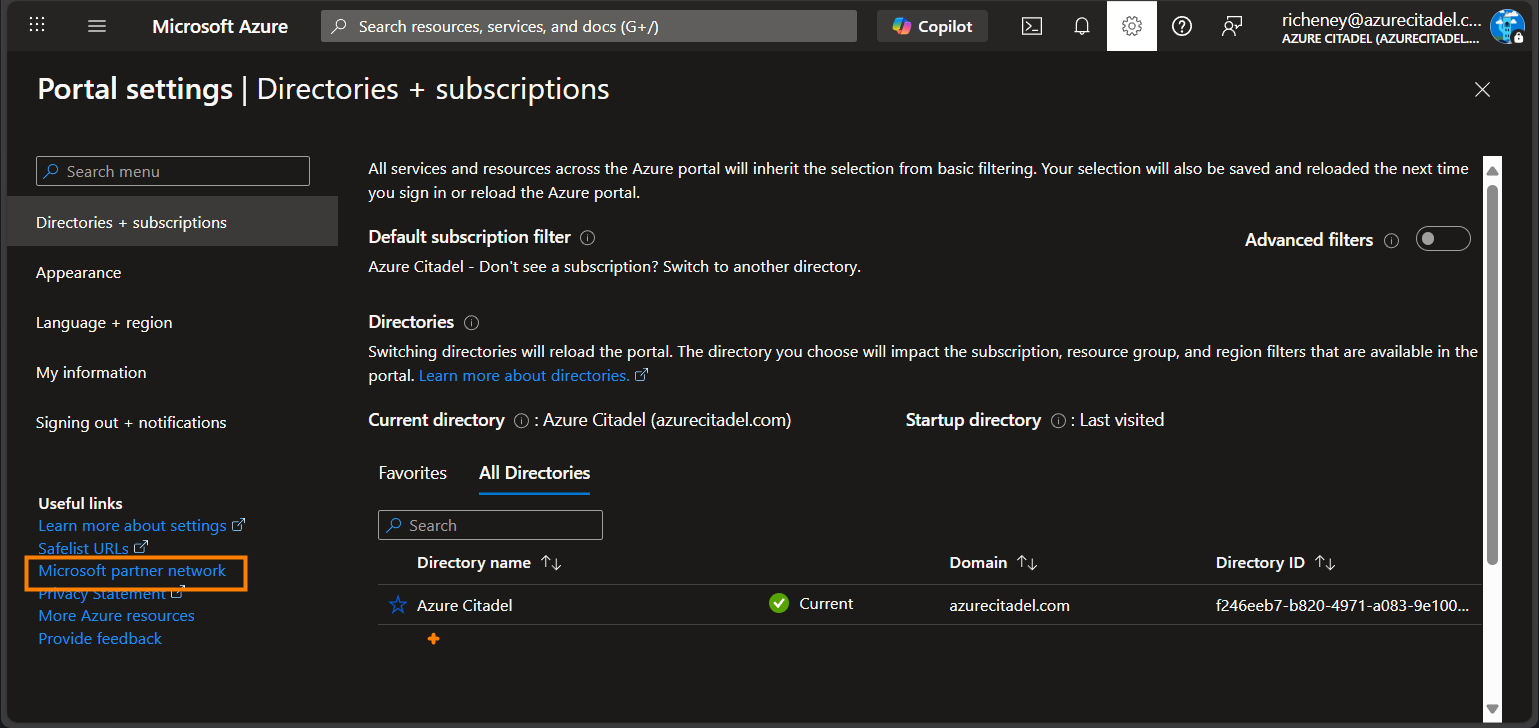
Open the Azure Portal.
-
Click on the Settings icon at the top.
-
Select the Microsoft partner network link in Useful Links at the bottom left.
-
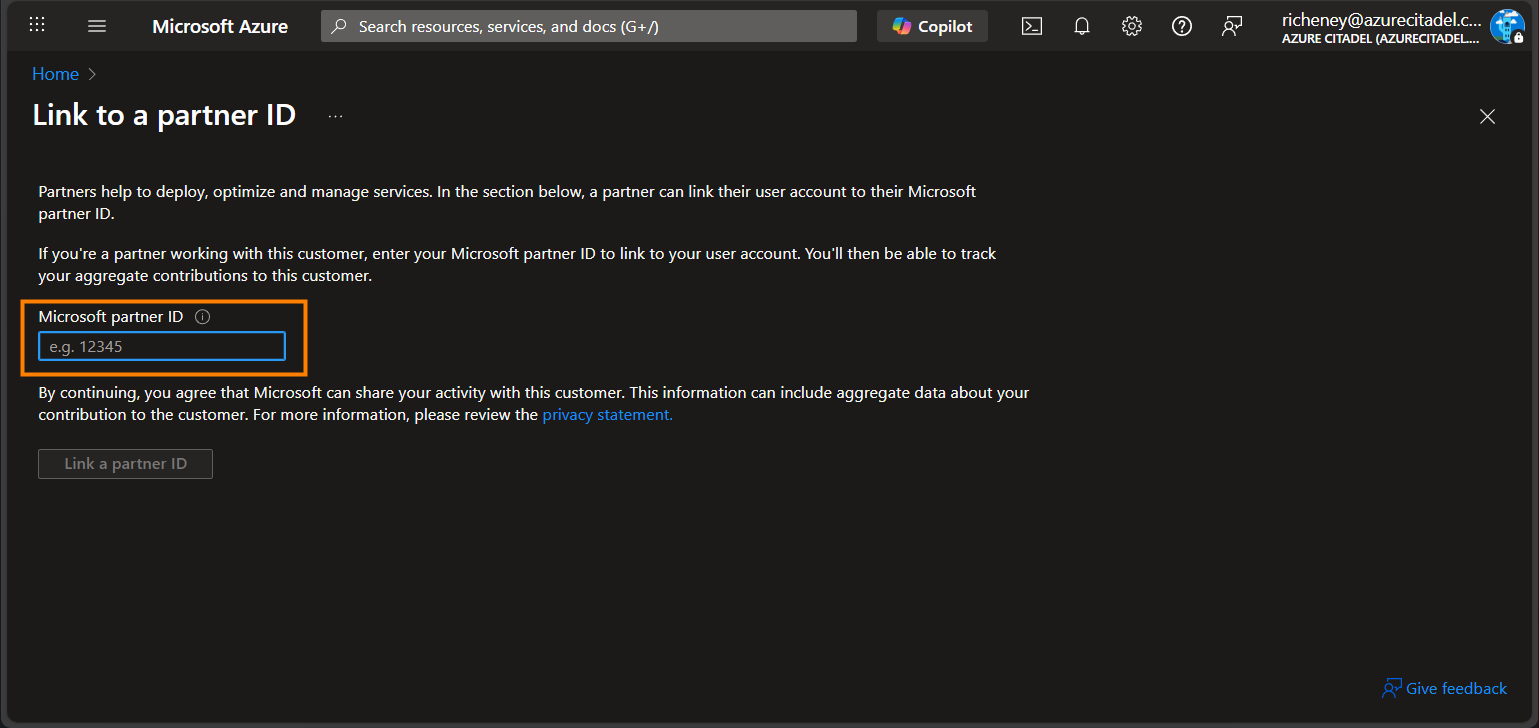
Enter your Partner ID.
-
Click on the Link a partner ID button to save.
Use PowerShell to create the link
-
Install the Az.ManagementPartner PowerShell module.
Install-Module -Name Az.ManagementPartner -Repository PSGallery -Force -
Sign in to the customer’s tenant.
Connect-AzAccount -TenantId <tenantId> -
Create the Partner Admin Link.
New-AzManagementPartner -PartnerId <partnerId> -
Additional commands
Display the partner ID.
Get-AzManagementPartnerUpdate the partner ID.
Update-AzManagementPartner -PartnerId <partnerId>Delete the Partner Admin Link.
Remove-AzManagementPartner -PartnerId <partnerId>
Use the Azure CLI to create the link
-
Install the Azure CLI’s managementpartner extension.
az extension add --name "managementpartner" -
Sign in to the customer’s tenant.
az login --tenant "<tenantId>" -
Create the Partner Admin Link.
az managementpartner create --partner-id "<partnerId>"
{
"createdTime": "2026-02-16T14:44:35.818407Z",
"etag": 9,
"id": "/providers/microsoft.managementpartner/partners/314159",
"name": "314159",
"objectId": "84964f8f-22ce-4a1e-ba9d-1e45a53ca1c4",
"partnerId": "314159",
"partnerName": "Azure Citadel",
"state": "Active",
"tenantId": "ac40fc60-2717-4051-a567-c0cd948f0ac9",
"type": "Microsoft.ManagementPartner/partners",
"updatedTime": "2026-02-17T13:48:41.4676825Z",
"version": 9
}
Additional commands
-
Display the partner ID.
az managementpartner show -
Update the partner ID.
az managementpartner update --partner-id "<partnerId>" -
Delete the Partner Admin Link.
az managementpartner delete --partner-id "<partnerId>"
Why do you have to switch into each customer tenant for guest IDs?
Your user ID in your home tenant may have been invited as a guest to multiple customer environments. You are signing in with the same MFA each time, so why do you need to switch into each customer tenant and recreate the Partner Admin Link in each one?
When you accept an invitation, Entra creates a new objectId in the customer’s tenant. (The User Principal Name for a guest ID includes #EXT#, e.g. first.last_partner.com#EXT#@customer.com.)
The Partner Admin Link is between the tenantId.objectId and the partnerId as you can see in the JSON output above for the Azure CLI commands.
Attestation
I have created a Bash script, pal_attestation.sh, that you are free to use if it helps you to display information about Partner Admin Link. This is useful if you need to copy and paste the output to prove that a link is in place for that customer context. You can copy and paste the output, pipe it through to jq, or redirect to a file.
A few example usages are shown below for displaying
- the core info (for the tenant, the security principal, and the Partner Admin Link)
- the core info, plus direct RBAC role assignments (note the caveats)
- the core info for another objectId and its RBAC role assignments
You first need to authenticate and ensure that you are in the correct customer context.
This Bash command will work in the Cloud Shell, even in the PowerShell experience.
Core info
curl -sSL https://aka.ms/pal/attestation | bash
{
"tenantId": "ac40fc60-2717-4051-a567-c0cd948f0ac9",
"tenantDisplayName": "Contoso",
"tenantDefaultDomain": "contoso.com",
"type": "user",
"displayName": "Richard Cheney",
"userPrincipalName": "richard.cheney@azurecitadel.com",
"appId": null,
"objectId": "74afa9e2-d243-414b-bab2-db8dd242827f",
"partnerAdminLink": "/providers/microsoft.managementpartner/partners/314159",
"partnerName": "Azure Citadel",
"partnerId": "314159"
}
{
"tenantId": "ac40fc60-2717-4051-a567-c0cd948f0ac9",
"tenantDisplayName": null,
"tenantDefaultDomain": null,
"type": "servicePrincipal",
"displayName": "PAL (Partner Admin Link) for Azure Citadel",
"userPrincipalName": null,
"appId": "7b7fe81e-da85-4271-a065-b0a00634ae75",
"objectId": "a52475b0-d310-41ac-a4b1-d1e3161e0127",
"partnerAdminLink": "/providers/microsoft.managementpartner/partners/314159",
"partnerName": "Azure Citadel",
"partnerId": "314159"
}
Extended info with assignments
Note that this uses the resource graph to additionall get the direct RBAC role assignments.
It will not return secondary RBAC role assignments, e.g. via a security group’s role assignment. You will also not see any temporary assignments (e.g. via Privileged Identity Management or the Access Packages in Microsoft Entra ID Governance’s Entitlement Management) unless they are currently active.
curl -sSL https://aka.ms/pal/attestation | bash -s -- --assignments
{
"tenantId": "ac40fc60-2717-4051-a567-c0cd948f0ac9",
"tenantDisplayName": "Contoso",
"tenantDefaultDomain": "contoso.com",
"type": "user",
"displayName": "Richard Cheney",
"userPrincipalName": "richard.cheney@azurecitadel.com",
"appId": null,
"objectId": "74afa9e2-d243-414b-bab2-db8dd242827f",
"partnerAdminLink": "/providers/microsoft.managementpartner/partners/314159",
"partnerName": "Azure Citadel",
"partnerId": "314159",
"assignments": [
{
"scope": "/providers/Microsoft.Management/managementGroups/alz",
"id": "b25e4a12-2d7d-19b0-3de0-0f12895873ed",
"roleName": "Azure Landing Zones Management Group Reader (alz-mgmt)",
"roleType": "Custom"
},
{
"scope": "/subscriptions/a7484f13-d60f-4e5a-a530-fdaade38716a",
"id": "8e3af657-a8ff-443c-a75c-2fe8c4bcb635",
"roleName": "Owner",
"roleType": "BuiltIn"
},
{
"scope": "/subscriptions/a7484f13-d60f-4e5a-a530-fdaade38716a/resourceGroups/terraform/providers/Microsoft.Storage/storageAccounts/terraformfabric562b54eb",
"id": "ba92f5b4-2d11-453d-a403-e96b0029c9fe",
"roleName": "Storage Blob Data Contributor",
"roleType": "BuiltIn"
}
]
}
{
"tenantId": "ac40fc60-2717-4051-a567-c0cd948f0ac9",
"tenantDisplayName": null,
"tenantDefaultDomain": null,
"type": "servicePrincipal",
"displayName": "PAL (Partner Admin Link) for Azure Citadel",
"userPrincipalName": null,
"appId": "7b7fe81e-da85-4271-a065-b0a00634ae75",
"objectId": "a52475b0-d310-41ac-a4b1-d1e3161e0127",
"partnerAdminLink": "/providers/microsoft.managementpartner/partners/314159",
"partnerName": "Azure Citadel",
"partnerId": "314159",
"assignments": [
{
"scope": "/providers/Microsoft.Management/managementGroups/platform",
"id": "cfd33db0-3dd1-45e3-aa9d-cdbdf3b6f24e",
"roleName": "Support Request Contributor",
"roleType": "BuiltIn"
},
{
"scope": "/subscriptions/73568139-5c52-4066-a406-3e8533bb0f15",
"id": "cfd33db0-3dd1-45e3-aa9d-cdbdf3b6f24e",
"roleName": "Support Request Contributor",
"roleType": "BuiltIn"
},
{
"scope": "/subscriptions/a7484f13-d60f-4e5a-a530-fdaade38716a",
"id": "b24988ac-6180-42a0-ab88-20f7382dd24c",
"roleName": "Contributor",
"roleType": "BuiltIn"
}
]
}
Assignment info for another object id
This is useful to display assignments for another user or service principal.
Note that this will not return the Partner Admin Link information, as you must authenticate for the PAL REST API call to work.
curl -sSL https://aka.ms/pal/attestation | bash -s -- --assignments --object-id <object-id>
The script will handle being passed the app ID, or the object ID for the app reg, and will automatically determine the object ID for the service principal. If you do not want to see the stderr warning messages then add 2>/dev/null to the command.
{
"tenantId": "ac40fc60-2717-4051-a567-c0cd948f0ac9",
"tenantDisplayName": "Contoso",
"tenantDefaultDomain": "contoso.com",
"type": "user",
"displayName": "Richard Cheney",
"userPrincipalName": "richard.cheney@azurecitadel.com",
"appId": null,
"objectId": "74afa9e2-d243-414b-bab2-db8dd242827f",
"partnerAdminLink": "Unavailable",
"partnerName": "Unavailable",
"partnerId": "Unavailable",
"assignments": [
{
"scope": "/providers/Microsoft.Management/managementGroups/alz",
"id": "b25e4a12-2d7d-19b0-3de0-0f12895873ed",
"roleName": "Azure Landing Zones Management Group Reader (alz-mgmt)",
"roleType": "Custom"
},
{
"scope": "/subscriptions/a7484f13-d60f-4e5a-a530-fdaade38716a",
"id": "8e3af657-a8ff-443c-a75c-2fe8c4bcb635",
"roleName": "Owner",
"roleType": "BuiltIn"
},
{
"scope": "/subscriptions/a7484f13-d60f-4e5a-a530-fdaade38716a/resourceGroups/terraform/providers/Microsoft.Storage/storageAccounts/terraformfabric562b54eb",
"id": "ba92f5b4-2d11-453d-a403-e96b0029c9fe",
"roleName": "Storage Blob Data Contributor",
"roleType": "BuiltIn"
}
]
}
{
"tenantId": "ac40fc60-2717-4051-a567-c0cd948f0ac9",
"tenantDisplayName": null,
"tenantDefaultDomain": null,
"type": "servicePrincipal",
"displayName": "PAL (Partner Admin Link) for Azure Citadel",
"userPrincipalName": null,
"appId": "7b7fe81e-da85-4271-a065-b0a00634ae75",
"objectId": "a52475b0-d310-41ac-a4b1-d1e3161e0127",
"partnerAdminLink": "Unavailable",
"partnerName": "Unavailable",
"partnerId": "Unavailable",
"assignments": [
{
"scope": "/providers/Microsoft.Management/managementGroups/platform",
"id": "cfd33db0-3dd1-45e3-aa9d-cdbdf3b6f24e",
"roleName": "Support Request Contributor",
"roleType": "BuiltIn"
},
{
"scope": "/subscriptions/73568139-5c52-4066-a406-3e8533bb0f15",
"id": "cfd33db0-3dd1-45e3-aa9d-cdbdf3b6f24e",
"roleName": "Support Request Contributor",
"roleType": "BuiltIn"
},
{
"scope": "/subscriptions/a7484f13-d60f-4e5a-a530-fdaade38716a",
"id": "b24988ac-6180-42a0-ab88-20f7382dd24c",
"roleName": "Contributor",
"roleType": "BuiltIn"
}
]
}